DryvIQ was able to scan and identify Nicolet National Bank’s IT data, assess its sensitivity, and classify it accordingly – delivering accuracy rates up to 92 percent. In addition to a stronger security posture, Nicolet now has the intelligence to make decisions that can increase efficiencies in data management.
Make better, informed decisions faster — with data-driven intelligence
41% of business leaders lack understanding of their unstructured data because it’s complex or not accessible enough.
Unstructured data makes up over 90% of enterprise data, and it’s growing rapidly. Documents, emails, images, and other files often hold immense value that, without proper discovery and management, remains untapped. In fact, this data can become a liability, slowing AI adoption, increasing security risks, and limiting operational efficiency.
With DryvIQ’s intelligent data discovery, you can analyze and organize your entire unstructured data estate. It’s the foundational first step to creating business-ready data that accelerates decision-making, fuels AI-driven insights, and strengthens data governance. No matter the purpose or outcome, DryvIQ ensures your data is relevant, organized, clean, secure, and ready to power what’s next.
88% of organizations are no longer confident they can detect and prevent loss of sensitive data
DryvIQ’s sensitive data discovery solution automatically scans, classifies, and maps sensitive information across unstructured content – whether it’s stored on-premises or in the cloud. Our patented platform inspects the files’ contents to accurately detect personally identifiable information (PII), biometrics, employee credentials, sensitive IT data, financial information, intellectual property, and other high-risk data.
With advanced AI, configurable scans, and an extensive library of built-in classifiers and entity types, DryvIQ makes it simple to tailor data discovery initiatives to your business objectives, security frameworks, and compliance requirements. This deep visibility transforms unstructured data from a liability into a secure, well-governed business asset – ready to support AI initiatives, regulatory demands, and better decision making.

Between the speed and accuracy of the platform and working with the DryvIQ team, it’s just been incredible.
Accomplish more with insights into your most valuable data
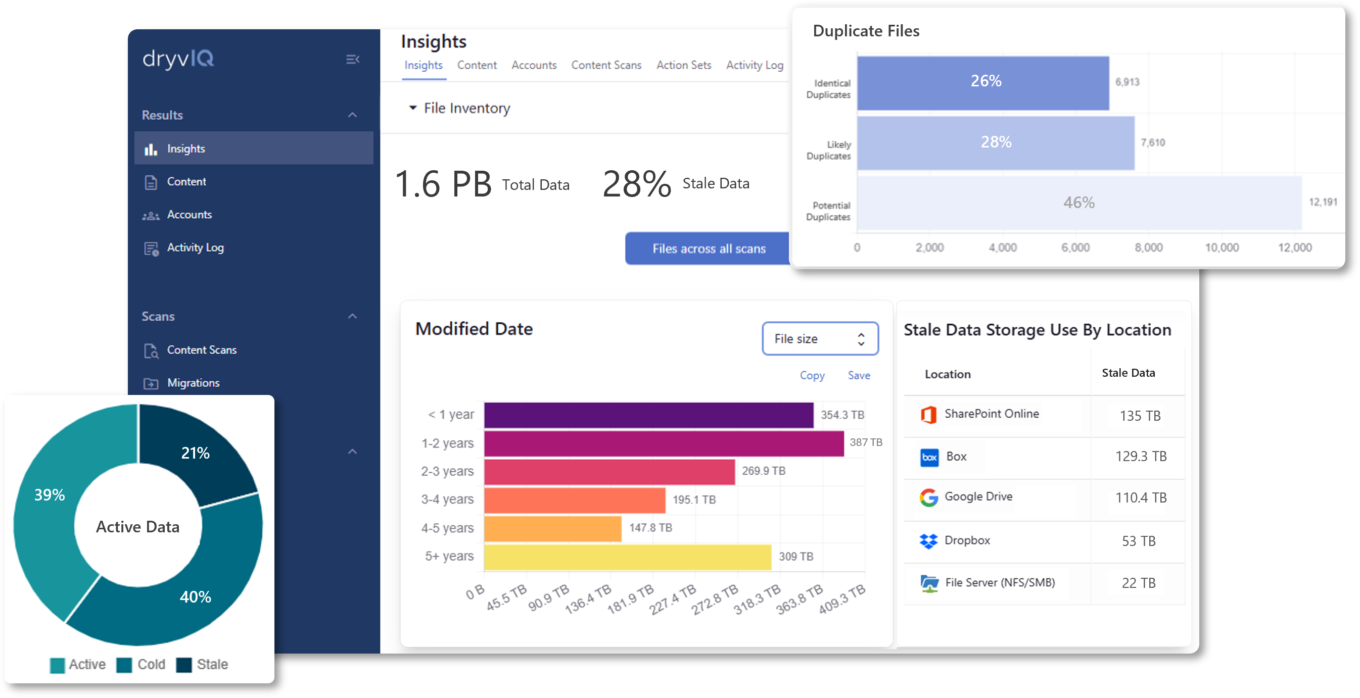
DryvIQ’s intelligent data discovery surfaces the insights you need to take control of your unstructured data. Go beyond basic file inventories and gain visibility into document types, labels, metadata, data age, last-accessed dates, storage locations, permissions, and both internal and external sharing rights.
DryvIQ pairs patented AI-driven discovery and classification with expert methodology to deliver deep, actionable insights at petabyte scale. Scan and analyze unstructured data across 40+ repositories — including NFS shares, Microsoft SharePoint, Teams, and OneDrive, Box, Google, Dropbox, and more — to reduce risk, locate sensitive information, and ready your data to work for you.
